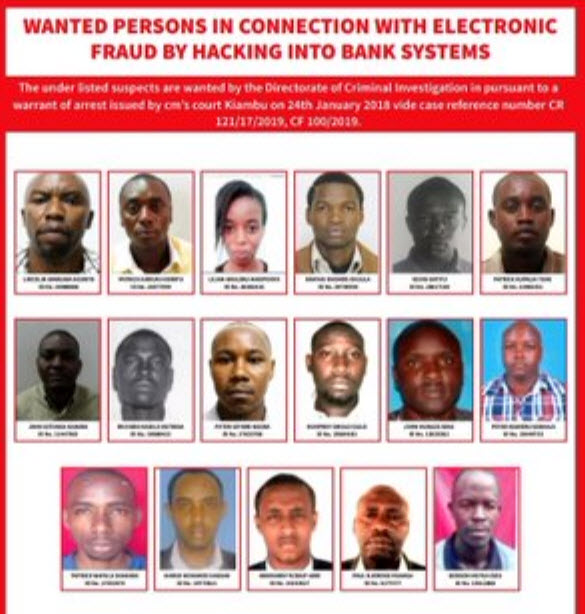
The Directorate of Criminal Investigations (DCI) on Wednesday published posters with the faces and names of 130 suspects wanted for hacking into bank accounts in Kenya.
It is hard to quantify how much has been lost to online hacking with banks not readily giving the information but according to the police, there are hundreds of cases and billions of shillings lost in the last year alone.
According to Dr. Bright Mawudor the head of cyber security services at Internet Solutions, more than 70% of the local banking applications are not safe with many of them containing loopholes that hackers can use to access your bank account.
“The banks are rushing to bring apps every other day competing for customers but what they are forgetting is the safety aspect of the systems once in place,” said Dr. Mawudor.
Dr. Mawudor demonstrated to Citizen Digital how easy it was to hack into a phone using a laptop and turning it into a monitoring device using its inbuilt camera.
According to him more than Ksh.50 million is lost through online bank fraud on a daily basis.
“It’s easy to hack into an account simply because there are no governance structures in place to protect consumers,”
While the Kenya Bankers Association admitted that there are leaks in the banks, they further state that banks have tried beefing up their security systems but there is more that can be done.
“Banks have done a lot but the fraudsters are also working to steal from Kenyans meaning they have to do a lot motte to protect customers,” Habil Olaka- CEO, KBA.
Olaka did not dismiss the possibility of bank employees working with the fraudsters to give them inside information.
“Banks are now conducting a more in-depth analysis of their employees to ensure that they do not employ thieves purporting to be genuine employees,” said Olaka.
There are some safety precautions you as an individual can take to ensure that you do not lose your hard earned money.
First you have avoid clicking on links sent to you via email or any other messaging platform.
Second is to avoid logging into wifi networks that are open without security measures.
Finally you must vet and interrogate all applications before downloading them on to your phone as they might be used to capture your information.
By Faizal Ahmed
![]()